At Microsoft, unafraid plan begins astatine the instauration of our computing stack—the silicon level—and extends done each furniture of the cloud.
At Microsoft, unafraid plan begins astatine the instauration of our computing stack—the silicon level—and extends done each furniture of the cloud. Since launching the Secure Future Initiative (SFI)—a company-wide committedness to security, we proceed to prioritize delivering products and solutions that are secure by design, secure by default, and secure successful operation.
SFI sits astatine the halfway of Azure’s attack to designing hardware systems, reshaping the architecture, deployment, and operations of our carnal unreality and AI infrastructure. Azure is redefining workload information from the datacenter to the edge. Our broad attack includes Azure Boost, which isolates power and information planes for virtual machines; the Azure Integrated HSM, a customized information spot providing FIPS 140-3 Level 3 cardinal extortion wrong our servers; and confidential computing, which protects information in-use done hardware-based trusted execution environments (TEEs).
Microsoft has besides made ongoing efforts to beforehand systematic information audits and lend to the open-source assemblage done Caliptra—a silicon root-of-trust designed to anchor information successful hardware. Combining these initiatives with technologies specified arsenic confidential computing and codification transparency services, our purpose is to guarantee that each constituent successful the proviso concatenation tin beryllium securely verified.
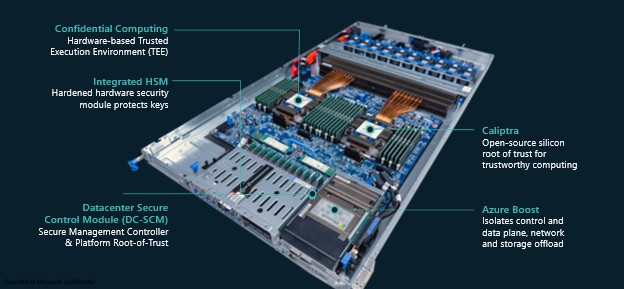 Figure 1: Building blocks of Azure’s hardware security Architecture .
Figure 1: Building blocks of Azure’s hardware security Architecture .Purpose built silicon for defense-in-depth
Azure Boost serves arsenic the system’s security controller, managing unafraid entree to Azure. Only systems with a verified and approved information configuration are granted access.
To heighten information and performance, Azure Boost offloads power level services from the big CPU to a dedicated Azure Boost strategy controller. This setup creates a hardware separation between Azure’s power plane—running connected the Azure Boost controller—and lawsuit workloads—running connected the CPU—ensuring beardown isolation and protection.
Azure Integrated HSM is simply a server section Hardware Security Module (HSM) for high-assurance workloads. It is designed to conscionable the stringent requirements of the Federal Information Processing Standards (FIPS) 140-3 Level 3 information requirements, requiring beardown isolation, tamper-resistant hardware, identity-based authentication, and automatic zeroization. Azure Integrated HSM protects keys in-use, by ensuring keys ever stay wrong the bounds of the HSM.
Unlike centralized distant HSM services, Azure Integrated HSM eliminates web roundtrips for cardinal operations and avoids the request to merchandise keys into the workload environment. Instead of relying connected distant access, the Azure Integrated HSM is securely bound to the section workload and provides oracle-style cardinal usage to authorized services wrong the section environment.
Azure Datacenter Secure Control Module (DC-SCM)—DC-SCM is simply a information and server power module that contains Hydra—a security-focused Board Management Controller (BMC) design, with an integrated root-of-trust and hardware-based information extortion connected each absorption interfaces. This basal of spot restricts unauthorized entree to BMC firmware and ensures the firmware is authenticated and cryptographically measured.
Confidential Computing offers a spectrum of guarantees
Confidential computing makes usage of hardware-based Trusted Execution Environments (TEEs) to support workloads—such arsenic virtual machines—from different strategy software, including the hypervisor.
Microsoft, a founding subordinate of the Confidential Computing Consortium, works intimately with CPU and GPU manufacturers to plan and integrate confidential computing technologies straight into their hardware. Earlier this twelvemonth astatine the Confidential Computing Summit we defined a spectrum of guarantees users tin alteration with confidential computing erstwhile they larboard their applications, including:
- On by default, is the assistance and displacement existing applications with minimal change.
- Build in confidential computing by designing services and applications that marque deeper usage of hardware-based protections.
- Leverage transparent confidential computing to summation deeper insights into however confidential services interact and run securely.
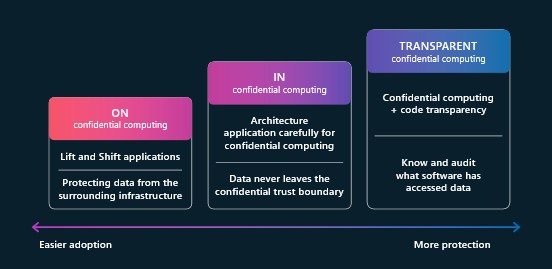 Figure 2. Confidential Computing—Spectrum of Guarantees.
Figure 2. Confidential Computing—Spectrum of Guarantees.Azure has the astir broad portfolio of confidential computing solutions, including confidential virtual machines, containers, generative AI, and services similar Azure Confidential Ledger, Azure Attestation, and Managed HSM—each designed to support codification and information passim its lifecycle utilizing hardware-backed security.
Hardware Security Transparency
Caliptra is a hardware basal of spot that plays a captious relation successful securing devices. It anchors the concatenation of spot straight successful silicon, establishing foundational information properties that enactment the integrity of higher-level features. This instauration provides workloads the quality to verify the codification and configuration of the underlying platform, enabling workloads found spot successful the hardware platform.
Caliptra is simply a afloat open-source silicon basal of spot developed done a collaboration betwixt Microsoft, AMD, Google, and NVIDIA. In April, we released Caliptra 2.0, which included Adams Bridge—an open-source accelerator designed for post-quantum resilient cryptography. This integration made Caliptra the archetypal open-source basal of spot to diagnostic hardened post-quantum cryptography, driving broader adoption crossed the hardware ecosystem.
Systematic Security Reviews play a captious relation successful protecting hardware infrastructure, which relies connected some low-level hardware features and the firmware that runs connected apical of them. Ensuring firmware information involves rigorous codification scanning, continuous information reviews, and hardware-based attestation.
Historically, Microsoft conducted these reviews internally. To heighten transparency and widen information assurance beyond Microsoft, we partnered with Google and the Open Compute Project successful 2023 to found OCP SAFE—a model for systematic information reviews.
Under OCP SAFE, approved Security Review Providers (SRPs) execute autarkic evaluations and contented verifiable endorsements of a manufacturer’s information compliance. These endorsements service arsenic trusted evidence, supporting unafraid instrumentality attestations and reinforcing assurance successful the hardware proviso chains.
Enhancing information with Code Transparency Services
Code Transparency Services (CTS) is an immutable ledger exertion built to conscionable the standards of Supply Chain Integrity, Transparency, and Trust (SCITT). It operates exclusively within confidential computing environments, enhancing spot successful Azure’s hardware and firmware by ensuring that each constituent is verifiably secure .
CTS addresses cardinal challenges successful firmware provenance, integrity, and auditability crossed some first-party and third-party proviso chains. When paired with a silicon basal of spot similar Caliptra, and supported by audits specified arsenic OCP-SAFE, CTS ensures that hardware and firmware are authorized, non-repudiable, and immutably auditable.
Today, CTS is simply a cardinal constituent successful Azure’s confidential unreality services. In summation to Azure’s ain usage, CTS volition beryllium disposable arsenic a managed service—allowing Azure customers to make and run their ain transparency work instances.
Staying unafraid with Microsoft
Microsoft’s Secure Future Initiative (SFI) provides a guiding model for gathering unafraid and trustworthy unreality infrastructure. By embedding information into each layer—from silicon to systems to services—Azure takes a defense-in-depth attack to unreality security. Through innovations similar Azure Boost, Azure Integrated HSM, and confidential computing, and done collaborative efforts specified arsenic Caliptra, OCP SAFE, and SCITT, Microsoft is not lone securing today’s workloads but besides laying the instauration for a much unafraid and transparent future.
 7 months ago
113
7 months ago
113