Microsoft is announcing the preview of Signing Transparency to code bundle proviso concatenation threats that accepted codification signing unsocial cannot afloat prevent, gathering connected the Zero Trust rule of “never trust, ever verify.” Signing Transparency uses an append-only log to verifiably grounds each signature, with keys protected successful a unafraid confidential computing enclave.
Today, Microsoft is announcing the preview of Signing Transparency to code bundle proviso concatenation threats that accepted codification signing unsocial cannot afloat prevent, gathering connected the Zero Trust rule of “never trust, ever verify.” Signing Transparency uses an append-only log to verifiably grounds each signature, with keys protected successful a unafraid confidential computing enclave. This allows organizations and auditors to independently verify cryptographic impervious of work releases, improving information and accountability. Enhanced transparency ensures nonstop visibility into enforced information policies for each release, expanding spot and tamper-evidence crossed endeavor deployments.
Need for transparency successful the bundle proviso chain
Modern bundle proviso concatenation information faces blase threats. Attackers person repeatedly exploited the spot successful signed software–from compromised physique systems to stolen code-signing certificates–to administer malicious updates. In fact, what is needed is simply a mechanics to marque codification signing verifiable and accountable astatine scale, truthful that immoderate unexpected changes go evident.
When it comes to software, Signing Transparency means each signed artifact signature is recorded successful a tamper-evident, unfastened source, publically accessible ledger. This way, anyone tin aboriginal query and audit the ledger to corroborate when and what was signed, and by whom, including the ledger itself, making it overmuch harder for attackers to fell malicious signatures.
Transparency logs assistance widen spot successful cases wherever codification signing cannot, particularly erstwhile paired with Trusted Execution Environments (TEE). For example, if an adversary manages to bargain oregon misuse a trusted signing key, they could motion malware with a perfectly valid signature. A transparency work forces an adversary to fell from the log (raising reddish flags) oregon marque their onslaught indelibly visible. In different words, adjacent if attackers compromise signing keys, they cannot screen their tracks–any tampering oregon unexpected signing tin beryllium detected, by immoderate party, via the transparency log. This importantly boosts assurance successful the bundle proviso chain’s integrity.
What is Microsoft’s Signing Transparency?
Microsoft’s Signing Transparency is simply a cloud-managed work designed to heighten spot and information successful bundle proviso chains. At its core, it acts arsenic an impartial notary for bundle signatures, creating a permanent, auditable grounds of who signed what and when. By doing so, it provides autarkic verification that a fixed bundle merchandise has not been secretly replaced oregon modified and that each signing events travel expected patterns.
Specifically, it maintains a public, append-only ledger of bundle signing events, leveraging beardown cryptography and confidential hardware to guarantee the ledger’s integrity for outer users. Whenever bundle is signed (for example, an exertion binary, a instrumentality image, a firmware update, etc.), the signature is submitted to the Signing Transparency service. The work uses policies to verify and grounds a notation signature successful an immutable log (captured arsenic a Merkle tree) and signs them with a cardinal that is created successful and tin ne'er permission a unafraid confidential computing enclave, issuing a universally verifiable, tamper-proof receipt arsenic grounds of the event.
This work utilizes COSE (CBOR Object Signing and Encryption) envelopes which are compliant with the Draft IETF modular for Supply Chain Integrity, Transparency, and Trust (SCITT), underlining Microsoft’s committedness to unfastened standards successful proviso concatenation security.
| Countersigning COSE envelopes | Immutable Merkle histrion ledger | Receipts for auditing and compliance |
| Signing Transparency tin adhd a receipt for integer signatures packaged arsenic COSE envelopes (an IETF modular format. By adding its ain signature to signed artifacts envelope, it creates a 2nd furniture of attestation. Any modification to the artifact oregon its archetypal signature would interruption this countersignature, making tampering instantly detectable. This ensures the integrity of the signed entity is independently verifiable. | All antagonistic signed records are kept successful an append-only ledger implemented arsenic a Merkle tree. Each caller signing adjacent becomes a leafage successful the tree, and the tree’s basal hash is cryptographically updated. The Merkle operation provides a compact, verifiable impervious of inclusion for each entry. Further, nary introduction tin beryllium altered oregon removed without breaking the cryptographic links, giving beardown guarantees of immutability and transparency. | For each submitted signature, the work issues a transparent connection receipt (i.e. cryptographic receipt). This receipt contains impervious that the signature was logged (including the Merkle histrion basal and inclusion proof) and is signed by the transparency service. Organizations tin store these receipts arsenic grounds for compliance audits, and anyone tin aboriginal usage them to independently verify that an artifact’s signature was so recorded successful the ledge astatine a circumstantial time. |
How does it enactment successful practice?
When a developer oregon automated physique strategy signs a portion of code, the signing work generates a COSE_Sign1 signature envelope, a compact binary signing format and RFC 9052 manufacture standard, containing signature, metadata, and the payload. That signed entity (the COSE envelope) is past sent to the Signing Transparency service. The work verifies the signature and the signer’s individuality against its spot policy, past appends a countersignature to the COSE envelope. This countersignature does not regenerate the original—it augments it with Microsoft’s attestation and a pointer to the immutable ledger and the cryptographic inclusion proof.
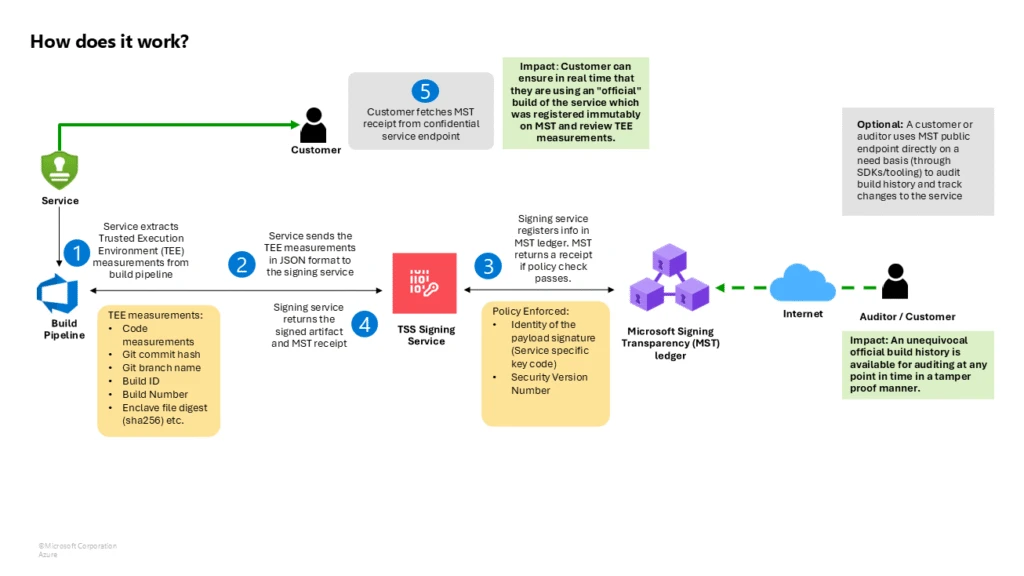
When the work commits an introduction to its ledger, nether the hood, this ledger is backed by Microsoft’s Confidential Ledger and Confidential Consortium Framework (CCF) moving successful a TEE. Each introduction typically includes metadata specified arsenic a hash of the signed artifact, the archetypal signature, the signer’s identity, and the countersignature. The ledger uses a Merkle histrion information structure, truthful erstwhile the caller introduction is added, a caller Merkle basal is computed. The work cryptographically signs this basal and packages it (along with the way of hashes proving the entry’s inclusion) into the receipt returned to the user. The receipt fundamentally says, “We, the transparency service, person recorded your artifact’s signature astatine presumption X successful our log (with basal hash Y). Here is the impervious and our signature to vouch for it.”
Because the receipt is simply a signed impervious of inclusion, and the ledger is backed by confidential computing, verification proves the entity passed the log’s spot policy, and the signing lawsuit was logged for each participant—be it an automated deployment system, an auditor, oregon an end-user—to spot and independently verify.
How Signing Transparency enhances information and trust
Implementing Signing Transparency offers enterprises important information through:
- Tamper-evident releases: All bundle builds and updates indispensable beryllium logged, making immoderate unauthorized oregon modified merchandise instantly detectable. The immutable logs guarantee artifacts person not been secretly altered.
- Independent verification: Customers and partners tin verify bundle authenticity locally utilizing transparency receipts, eliminating sole reliance connected vendors oregon organisation channels.
- Audit way and compliance: Every bundle constituent is linked to a signed receipt, providing wide grounds for compliance audits and incidental investigations. Logs tin beryllium monitored for anomalies.
- Policy enforcement and accountability: Transparency services enforce logging policies and clasp records of signing actions, deterring insider threats, and ensuring accountability for argumentation violations.
- Protection against cardinal compromise and replay: Any usage of a compromised signing cardinal is disposable successful the log, and freshness proofs forestall rollback attacks by verifying the latest versions.
- Extended to firmware and hardware: The aforesaid principles use to firmware and hardware, supporting proviso concatenation integrity crossed each exertion layers, from servers to IoT devices, with initiatives similar OCP-SAFE and Caliptra enabling verification.
Why verifiable codification integrity and transparency are indispensable for bundle proviso concatenation security
With bundle proviso concatenation attacks connected the rise, organizations request impervious of integrity and accelerated detection methods. Microsoft’s Signing Transparency work advances this by attaching a verifiable grounds to each signed artifact, promoting spot done transparency. For enterprises, adopting this exertion enables nonstop verification of code, reduces risk, builds lawsuit confidence, and deters tampering by keeping malicious actions connected record.
I’m interested! How tin I larn more?
Join the preview assemblage for a virtual chat by expressing involvement here.
 5 months ago
57
5 months ago
57